ಟ್ವೀಟ್ಗಳು
- ಟ್ವೀಟ್ಗಳು
- ಟ್ವೀಟ್ಗಳು & ಪ್ರತಿಕ್ರಿಯೆಗಳು
@davidben__ ತಡೆಹಿಡಿಯಲಾಗಿದೆ
ನೀವು ಖಚಿತವಾಗಿಯೂ ಈ ಟ್ವೀಟ್ಗಳನ್ನು ನೋಡಲು ಬಯಸುವಿರಾ? ಟ್ವೀಟ್ಗಳನ್ನು ನೋಡುವುದು @davidben__ ಅವರನ್ನು ತಡೆತೆರವುಗೊಳಿಸುವುದಿಲ್ಲ.
-
Some background and details on TLS 1.3, OpenSSL, Akamai. TLS1.3 FTW https://blogs.akamai.com/2017/01/tls-13-ftw.html …
-
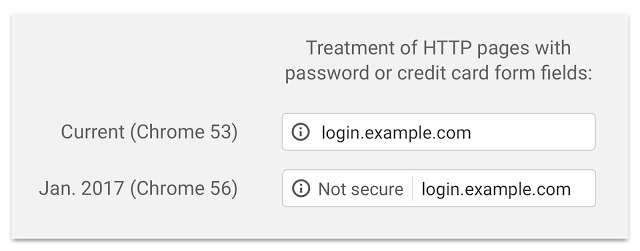
Still a little buggy, but you can try out chrome://flags/
#enable-http-form-warning in Chrome Canary to see HTTP warnings on autofill!pic.twitter.com/Ub97J5mIGZ
-
Anyone have a contact on Fortinet's firewall product? Could you have them mail davidben at google? (This is about TLS 1.3 compatibility.)
-
Use Chrome beta? If you're up to date, about half of you have TLS 1.3 (draft 18). Enjoy!
-
TLS 1.3 GREASE of Canary gets my Haskell TLS library oiled. :-)
-
Forever fuzzing of core open source software! Details here: https://testing.googleblog.com/2016/12/announcing-oss-fuzz-continuous-fuzzing.html … h/t
@kayseesee@halbecaf@mer__edith infernopic.twitter.com/znWnSOA5pe -
2017: The year Chrome plans to require Certificate Transparency for publicly trusted certificates https://groups.google.com/a/chromium.org/forum/#!topic/ct-policy/78N3SMcqUGw …
-
Intent to Deprecate and Remove: TLS CBC-mode ECDSA cipher suites in Chrome 56 https://groups.google.com/a/chromium.org/forum/#!topic/blink-dev/1eKb8bqT1Ds …
-
Dear servers, it is *not possible* to implement TLS 1.2 without SHA-2. Why are so many of you signing TLS 1.2 ServerKeyExchanges with SHA-1?
-
I'm so sad to see the return of "Opportunistic Encryption" for HTTPS. It's disingenuous and harmful to a secure web. Use U-I-R. Use HSTS.
-
Roughtime: a protocol for secure, auditable time synchronisation. https://www.imperialviolet.org/2016/09/19/roughtime.html …
-
Intent to Ship: GREASE for TLS (Generate Random Extensions And Sustain Extensibility) https://groups.google.com/a/chromium.org/forum/#!topic/net-dev/wJIj6SS68C8 …
-
Chrome will start marking some HTTP sites as non-secure beginning in January. Get ready! https://security.googleblog.com/2016/09/moving-towards-more-secure-web.html …pic.twitter.com/tBzz0E9lWh
-
Congratulations to the OpenSSL team on releasing 1.1.0, a huge milestone. https://www.openssl.org/news/openssl-1.1.0-notes.html …
-
Love our new Department of Chromeland security pins! h/t to
@metromoxie@lgarronpic.twitter.com/3Y7WDIVkE2
-
NSS can now run against BoringSSL's test suite! It's so great to see our tests be useful for a second TLS stack. https://www.ietf.org/mail-archive/web/tls/current/msg20793.html …
-
Pretty awesome to see non-Google QUIC deployments! https://groups.google.com/a/chromium.org/d/msg/proto-quic/IewtuSYH1vs/anySxbHSCgAJ …
-
Google enables HSTS for http://www.google.com - https://security.googleblog.com/2016/07/bringing-hsts-to-wwwgooglecom.html … KUDOS to Jay Brown for leading this effort.
-
If you try something three times and it does not work, don't do it a fourth time. I'd really like to be done with the TLS version fallback.
-
David Benjamin ಹಿಂಬಾಲಿಸಿದ್ದಾರೆ Kazuho Oku, Trevor Perrin, Catherine Olsson and 16 others
-
@kazuho
20 years' experience in network software development (mostly HTTP and Web-related, some proglang and database)
-
ಲೋಡಿಂಗ್ ಸಮಯ ಸ್ವಲ್ಪ ತೆಗೆದುಕೊಳ್ಳುತ್ತಿರುವಂತೆನಿಸುತ್ತದೆ.
Twitter ಸಾಮರ್ಥ್ಯ ಮೀರಿರಬಹುದು ಅಥವಾ ಕ್ಷಣಿಕವಾದ ತೊಂದರೆಯನ್ನು ಅನುಭವಿಸುತ್ತಿರಬಹುದು. ಮತ್ತೆ ಪ್ರಯತ್ನಿಸಿ ಅಥವಾ ಹೆಚ್ಚಿನ ಮಾಹಿತಿಗೆ Twitter ಸ್ಥಿತಿಗೆ ಭೇಟಿ ನೀಡಿ.


 Rich Salz
Rich Salz
 Emily Stark
Emily Stark
 David Benjamin
David Benjamin
 山本和彦
山本和彦
 Security Princess
Security Princess
 Ryan Sleevi
Ryan Sleevi
 Eric Lawrence
Eric Lawrence
 Adam Langley
Adam Langley
 Adrienne Porter Felt
Adrienne Porter Felt
 Nick Sullivan
Nick Sullivan
 William Chan
William Chan
 Ryan Hurst
Ryan Hurst

