Cybersecurity experts have warned about the North Korean hacker collective Lazarus. Despite the Log4Shell vulnerability (CVE-2021-44228) being patched over two years ago, Lazarus has continued…
Posts published in “Security”
Welcome to the Security zone, your go-to resource for all things related to digital safety. Here, you'll find a mix of topics like data encryption, firewall configuration, and best practices for avoiding phishing scams. We aim to offer straightforward guides to help you navigate the often confusing landscape of online security.
In addition to core topics, we also explore emerging security trends and the latest threats you should be aware of. We cut through the technical jargon to deliver clear, actionable advice. Whether you're a casual internet user or an IT professional, there's something here to help you beef up your digital defenses.
A significant security breach has been reported concerning Ledger's cryptocurrency management software. According to a tweet from banteg, a notable figure in the cryptocurrency community,…
Zoom, the popular video conferencing platform, has recently updated its software across multiple platforms to address a range of security vulnerabilities. These issues, spanning desktop…
A critical flaw in Apache Struts is being actively exploited by attackers globally, according to warnings from both Australian and French officials who anticipate widespread…
A significant security flaw in Windows allows attackers to gain control of systems just by dispatching a harmful email. The recipient doesn't have to open…
A critical Bluetooth vulnerability, designated as CVE-2023-45866, has been identified, enabling attackers to impersonate a keyboard and remotely take over various systems. This flaw affects…
Microsoft has updated its Edge browser to version 120, addressing multiple security issues unique to Edge and those inherited from the Chromium base. Among these,…
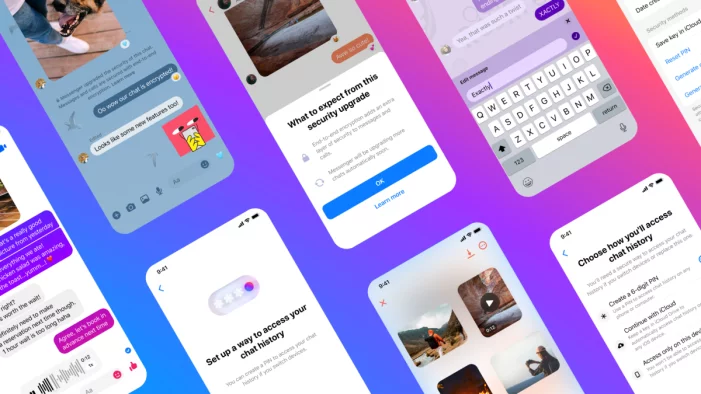
In a recent news bulletin, British police expressed significant disappointment following Meta's decision to implement end-to-end encryption by default for private chats and phone calls…
A group of security researchers have identified a series of vulnerabilities in Google Chromecasts. The vulnerabilities, if exploited, could allow attackers to install rogue firmware…
A U.S. senator has brought to light the covert surveillance tactics used by unidentified governments to track smartphone users. According to a report first disclosed…
23andMe, the personal genomics and biotechnology company, has been trying to contain a security breach that was first disclosed on October 6th. On October 19th,…
Microsoft has just announced a significant extension to the life of Windows 10, with an offer that will resonate with both organizations and individual users.…